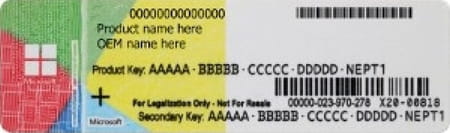
Back toprinter nightmare on Microsoft Windows: After the bug classified as CVE-2021-1675 and partially fixed in early June 2021, the new bug has now been discovered CVE-2021-34527 which is very similar and has been renamed “PrintNightmare“. Again it is a dangerous one security bug, which allows hackers to execute malicious code on Windows PCs.
Unfortunately, at least at the moment, even Microsoft didn't understand how dangerous PrintNightmare really is so much so that it has not yet assigned a severity index to it (which is usually done to indicate which are the potentially most dangerous bugs). Microsoft, however, says it is aware of the bug and is hard at work finding one solution. In the meantime, he invites everyone to update the operating system (all versions of Windows are affected by the bug, not just Windows 10) with the security patches released in early June to correct the previous bug CVE-2021-34527 and to follow some prevention measures that they can mitigate the risk of attack by a hacker.
How PrintNightmare works
The PrintNightmare bug derives from an error in the code of the so-called Windows Print Spoiler, that is that part of the operating system that deals with routing all calls to the printer and routing documents to this device.
The problem mainly affects servers and corporate networks, but in theory any computer connected to a network that has been attacked by exploiting the bug could also be attacked.
It could and, perhaps, it already was because according to Microsoft itself the bug PrintNightmare has already been exploited at least once.
How to defend against PrintNightmare
PrintNightmare doesn't have one yet security patches, so there isn't an update dedicated to it that closes the flaw once and for all. Microsoft, however, invites system administrators and ordinary users of all versions of Windows to update their operating systems.
On June 8, Microsoft released an update to fix the previous press spoiler bug and, according to the Redmond company, this upgrade is among the mitigation measures useful to limit the risks deriving from the new PrintNightmare.
Another useful measure is to disable the print spoiler, which is the gateway for potential hackers. The problem is that by turning off the spoiler the printer will no longer work. Alternatively, it is possible to disable remote printing, that is the service that allows you to print (within a company network) a file sent from another computer. This maneuver, however, is the responsibility of the network administrators and not the individual user.
Windows has a new dangerous bug: how to defend yourself