Il Remote Desktop Protocol (RDP) di Microsoft is still not sure, despite last year Microsoft released a patch to fix an important vulnerability, the CVE-2019-0887 reported by the cybersecurity company Check Point Technologies.
And it is Check Point that comes back to the charge because he found that, in the patch released by Microsoft, much of the problem was ignored rather than solved. For this reason, Check Point contacted Microsoft again, which could not help but admit the new vulnerability (largely the same as the previous one) by assigning it the code CVE-2020-0655. All of this as early as February, but the patch for this second vulnerability hasn't even been released in the recent May security updates. Much to the surprise of Check Point itself, which is now pulling Microsoft's ears.
What is Microsoft Remote Desktop Protocol
Il Remote Desktop Protocol is a proprietary protocol from Microsoft, which allows remote connection between computers through a convenient graphical interface. It is implemented via client, available for Windows, Linux, macOS, Android, iOS. In practice, this is the protocol required to use the utility Windows Remote Desktop Connection, very common both in business and for remote repairs of Windows computers.
Why the Remote Desktop Protocol is dangerous
Last year Check Point discovered that it was possible to perform a “Reverse RDP Attack“, that is remote code execution without user permission, through the RDP clients for the various operating systems. Check Point has tested both the official Microsoft client (i.e. its Remote Desktop), as well as other open source clients such as rdesktop and FreeRDP. Microsoft had officially fixed this flaw (which depends on the protocol and not just the client), but in reality this is not the case because Check Point found another way to bypass the patch and execute malicious code via RDP clients.
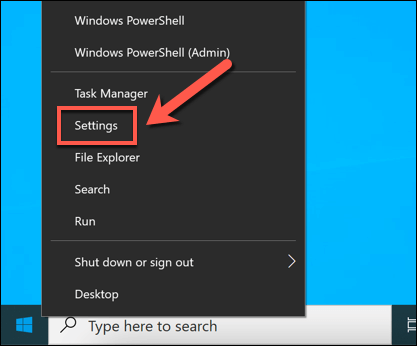
What to do in order not to risk
Since the problem is still there, Check Point does not miss the opportunity to point out that "It is a mystery that such a simple bypass went unnoticed for so many years in the sanitization process of Microsoft's main core". The board of the security company is to install the Microsoft patch to close at least one of the vulnerabilities. Check Point also asks individual client developers to act on their software until Microsoft decides to actually close the flaw at the protocol level.
Windows 10, Remote Desktop can put your data at risk